Germany, the main target of increasing spam mails worldwide
Every 7th dangerous spam mail went to German users
How acute is the danger?
According to a recent Kaspersky-Labs study, spam levels in email traffic were 58.31% last year, an increase of 3.03 percent compared to the year before. According to the study, most dangerous or harmful spam mails went to Germany. With 14.3%, this is about every seventh e-mail worldwide. The most common malicious attachments sent were Trojans that loaded ransomware onto the affected computers after opening. One of the leading malware programs was Locky, which received a lot of media interest due to its frequency and procedure.
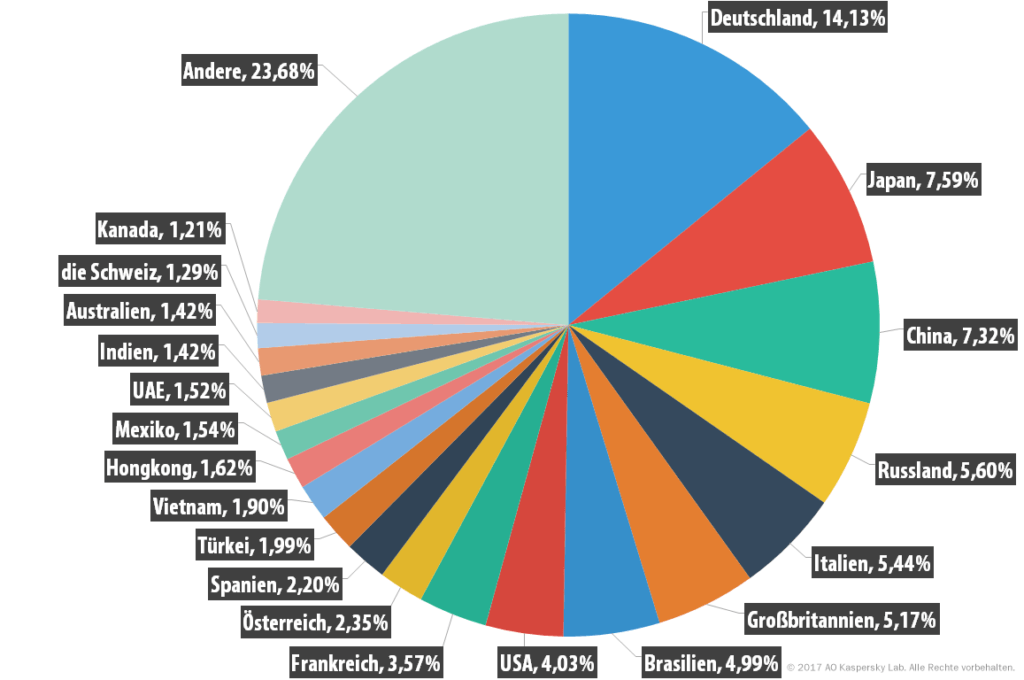
Source: Kaspersky
The forecasts published by Kaspersky after the survey indicate that this trend of growth will continue in the following year. Furthermore, the increase in e-mails containing malicious blackmailing software is one of the most significant changes in spam mails, which were previously known primarily for annoying and sometimes unfair but relatively harmless advertising.
According to Kaspersky, phishing scammers and other data theft methods no longer rely solely on spam mails, but use "all possible ways to contact their potential victims: SMS, advertising and social networks". In this way, an attempt is made to obtain further user data in order to be able to attack the user even more effectively afterwards.
Spam and fraud mails are sent periodically in extreme numbers before major events and festivals such as Christmas, New Year's Eve, Easter, etc. Please pay attention to the e-mails and especially attachments you intend to open during these times!
10 practical tips to detect malicious emails before they can cause problems:
- Turn off automatic downloading and displaying of "content from the Internet" (images, animations, etc.) in your mail program either generally or only for the senders you trust completely. Some programs also offer the setting "Display as plain text", which also provides this functionality.
- Deactivate the reading area (preview) in your mail program so that no content is displayed (and thus loaded) in your inbox before you open the email.
- Before opening an email, check the sender or sender address. However, it is also possible to forge the sender's name. If the explicit sender address is not currently displayed in the overview of your inbox, you must add this column.
- Always check the subject before opening the email. Subject lines such as "Generika for low prizes" or "Hi love, my name is... do you want to meet me?" are unlikely to contain serious content.
- Another indication for spam mails can be the salutation right at the beginning of the email content. Does it say your full and real name or just something like "Dear Customer" or "Dear Ladies and Gentlemen"?
- Is the content coherent and written in "familiar" language or does it contain excessive spelling and grammatical errors?
- Is there an imprint in or at the end of the message? Of course, this can also be "copied" very easily, but it is an additional indication.
- Does the email contain links to any other online content? Just call it up carefully and be warned: The link text says absolutely nothing about where the link leads to! For example, click on the following link: www.google.de (Don't worry! It just opens the Webmedia home page in a new tab :-)
- Take special care with all kinds of attachments and files that are offered for download! Especially for executable or packed files with the extension "exe", "zip" or "rar". In the past, Word documents (doc) or PDF files were also "carriers" of viruses and other malware. Open it only if you know the source and trust it without hesitation!
- However, if you accidentally open a dubious mail or an infected attachment, it is hoped that an up-to-date security program is installed that detects the threat and removes it in the best case.
You are not (really) sure?
Unfortunately, we often find that small, medium-sized and even large companies do not have sufficient protection and that nobody is responsible for managing and regularly reviewing security standards. As long as nothing happens, this will not be noticeable... However, if an "emergency" occurs, the effort and costs involved in recovering data can become exorbitant. In the worst case, your data will be irretrievably lost without appropriately secure backup solutions. If you are not sure whether your current solution would also cover the "worst case", please contact us. We would be pleased to check the actual situation, inform you about possible weak points and offer solutions that meet the requirements.
 German
German English
English